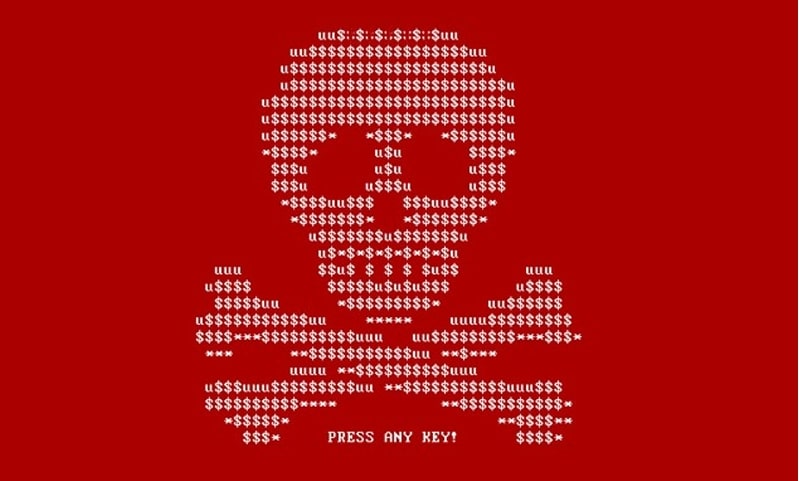
The start of 2017 was marked by the appearance of ransomware which impacted major French and international organizations. However, even if we all understand the extent of the threat, it is harder for us to understand how it appears.
That’s why TradOnline chose to speak with Vincent Philippot about the security of your data.
Hello, Vincent. You are the director of Lankaz, a service company working with freeware.
What is the scope of your activity?
Hello, Alice. We have a very wide scope of activity. Lankaz helps its customers from the most basic support to the implementation of high-availability IT infrastructure.
We are an external IT service provider (manpower, competencies, machines, and software).
Cryptovirus, ransomware, computer viruses, phishing, what are the real meanings hidden behind all the jargon?
Behind these terms hide digital tools used to capitalize on information, money, or processing power.
These tools use different vectors to propagate themselves, like software flaws, the naivety of a worker, an email with false visual identity or content.
These programs are created by governments, criminal organizations, conmen, and sometimes by enthusiasts for research purposes or out of simple curiosity.
Are your clients often concerned with data security?
Yes, it’s a request we receive more and more frequently, especially since the Edward Snowden revelations. Before, for a lot of SMEs data security just meant having an archiving / back-up strategy.
Companies have finally started to realize the importance of digital security and, above all, of their choice of partners.
I imagine there are “common sense” and more complex solutions to fight malware on the web, what basic advice could you give to the average employee?
Without going into security policies, which absolutely must be discussed and implemented in a company, an employee can:
– Systematically make their IT service aware of even the smallest doubts.
– Pay attention to email senders and the file formats of attachments.
– Avoid plugging in devices from external sources to their workstation (external hard drives from home, etc.) and vice versa.
– Update their entire suite of IT solutions or have them updated. An IT system is a living thing; abandoning it can raise a number consequential risks.
Now, in most cases, an average employee is relatively limited by what actions they can take on their PC. It is absolutely necessary that the director sets up solutions like:
– Increase the storage drives, back-ups and externalize all their data.
– Management of the IT suite and rights on workstations.
– A filtering proxy that allows for access to malicious sites to be cut off completely and easily (thanks to lists managed by companies or communities).
– Firewall / antivirus / Intrusion Detection System
– An incident management process…
For all the rest, they mustn’t hesitate to request the help of professionals!
Concerning e-mail service security, what solutions do you propose to SOHO and SME clients, like TradOnline?
E-mails are a gateway for the propagation of many of these viruses and malware. Therefore, they require particular attention.
Our e-mail solutions are standardized. We use free / Open source tools, both because we believe in the ideology of these solutions and also because of the level of control that they allow us to have.
More specifically, the antivirus and antispam are managed by a community which is made up of companies, major organizations, and enthusiasts. So, using a malicious sender as an example, we take advantage of the entire community and their responsiveness.
The antispam also has the capacity for self-learning. So, all the e-mails listed as spam are automatically analysed in order to create filtering rules without requiring further input from the user.
Specifically concerning TradOnline, I can tell you that today, 256 e-mails containing viruses (including at least a few with ransomware) were directly eradicated at their source. 🙂
Often, the machines used by these malicious spam/virus senders are compromised. An e-mail service solution is able to consult the list of servers authorized to send for a domain name.
If a machine isn’t authorized -> the mail goes directly to the spam folder.
In short, I’d have to write a white paper to fully respond to this question!
According to a recent survey (the full white paper is available in English), 60% of French organizations prefer a primarily training-based approach to deal with ransomware. Is this a trend that you agree with?
Yes, that’s a fact. Working with American, German, and French companies, it’s clear that the approach isn’t the same.
In my experience, American companies take radical approaches, whether it is bothersome for the employees or not. Security is their foremost concern, and they invest accordingly (Software, hardware, and also training).
In France, it’s much quieter (outside of major corporations); there is a general ignorance of the risks. It seems to me like this is an observation phase.
Often enough, I hear “It has to be extremely secure”. However, since this often entails significant development costs, forethought, and the work of the entire company, few directors actually see the project through to the end.
Training is very important, and it’s the first stepping stone for French companies to understand the situation. It’s a great start! It’s important to understand that most security breaches don’t require a computer, just a bit of nerve, what we call “social engineering”. To protect against these practices, only training and awareness are effective.
Thank you, Vincent, for enlightening us a bit on this very technical subject.
If you’d like to contact Vincent Philippot, visit his site: https://www.lankaz.net/
He essentially travels around the Mayenne region, but is willing to make exceptions for new challenges!